Pipes
Enable your customers to connect their third-party accounts to your application.
Set up Pipes to let your users securely connect their third-party accounts to your application.
Configure a provider in the WorkOS Dashboard to make it available to your users.
Visit the Pipes section of the WorkOS Dashboard. Click Connect provider and choose the provider from the list. If you do not see the provider you need, reach out to our team.
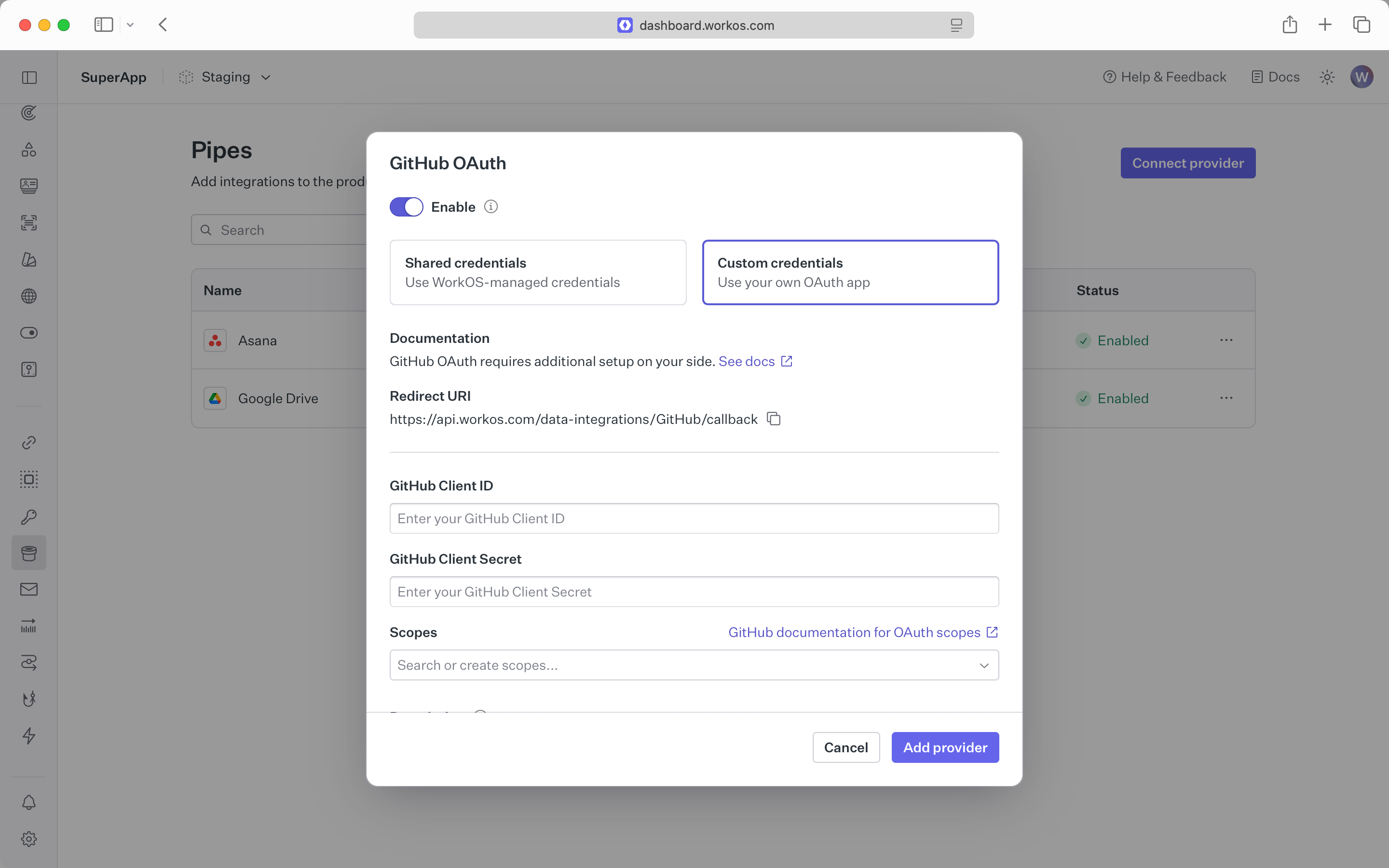
Use WorkOS-managed shared credentials in sandbox environments for the fastest setup. This allows users to connect immediately without requiring you to create OAuth applications with each provider.
- Specify the required scopes for your application.
- Provide an optional description. This will be used in the widget to inform users on how your application will use their data from the provider.
Configure the provider with your own OAuth credentials for production applications:
- Create an OAuth application within the provider’s dashboard.
- You can find instructions on setting up the provider in the documentation section of the setup modal.
- Use the provided redirect URI when configuring the provider.
- Set the client ID and secret from the provider.
- Specify the required scopes for your application.
- You may need to set these scopes in the provider configuration as well.
- Provide an optional description. This will be used in the widget to inform users on how your application will use their data from the provider.
Commonly used scopes are provided in-line, but you should consult each provider’s documentation for the full list of available scopes.
Use the Pipes Widget to give users a pre-built UI for connecting and managing their accounts. The widget shows available providers and lets users initiate the authorization flow. It communicates with the WorkOS API and stores the connection information for the user. If a problem occurs with the user’s access token, the widget notifies them to reauthorize.
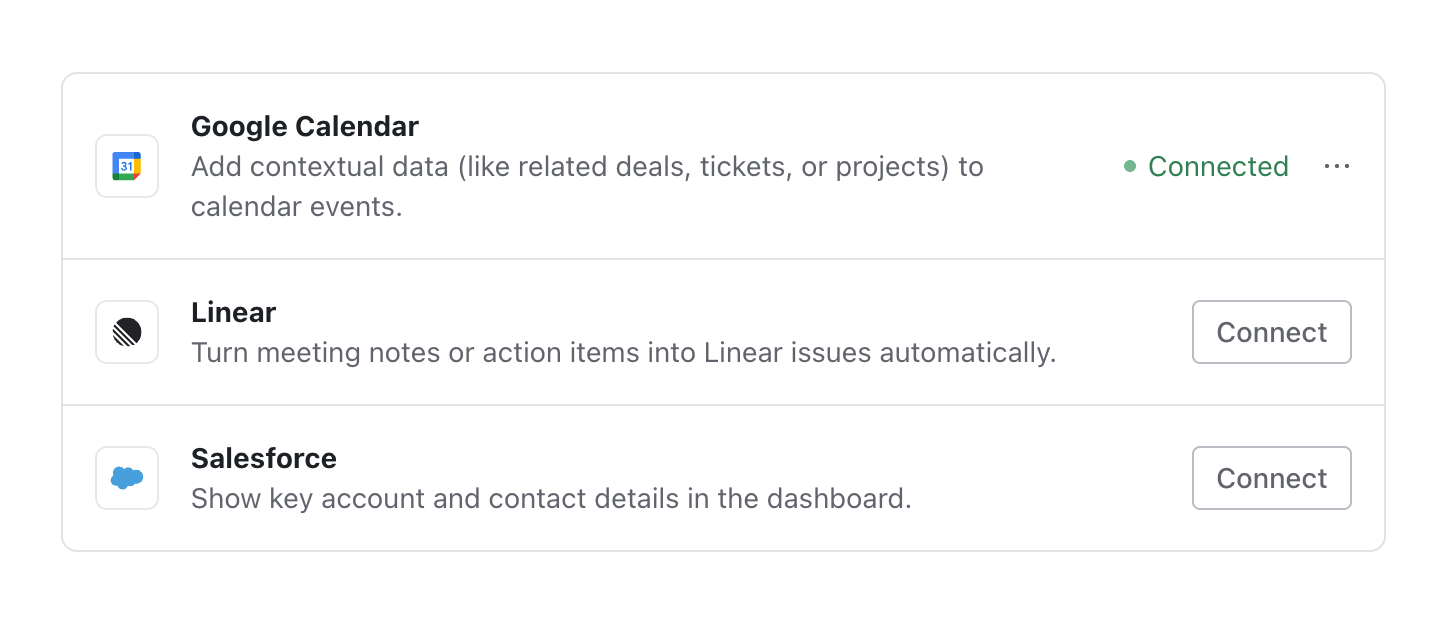
The description in the widget is set in the provider’s configuration in the WorkOS Dashboard.
After a user connects a provider, fetch access tokens from your backend to make API calls to the connected service on their behalf. Pipes handles token refreshing automatically, so you always receive a fresh token. If a problem occurs with the token, the endpoint returns information about the issue so you can direct the user to correct it. This may require sending the user to reauthorize directly or via the page with the Pipes widget.
import { Octokit } from '@octokit/rest'; import { WorkOS } from '@workos-inc/node'; const workos = new WorkOS(process.env.WORKOS_API_KEY); async function getUserGitHubRepos(userId, organizationId) { const { accessToken, error } = await workos.pipes.getAccessToken({ provider: 'github', userId: userId, organizationId: organizationId, }); if (!accessToken) { // Handle error: user needs to connect or reauthorize console.error('Token not available:', error); return; } // Check if required scopes are missing if (accessToken.missingScopes.includes('repo')) { console.error('Missing required "repo" scope'); return; } // Use the access token with GitHub API const octokit = new Octokit({ auth: accessToken.token, }); const { data: repos } = await octokit.repos.listForAuthenticatedUser(); return repos; }